40-2 Vol. 3D
ENCLAVE EXITING EVENTS
In all cases, the choice of exit stack and the information pushed onto it is consistent with non-SGX operation.
Figure 40-1 shows the Application and Exiting Stacks after an exit with a stack switch. An exit without a stack
switch uses the Application Stack. The ERESUME leaf index value is placed into RAX, the TCS pointer is placed in
RBX and the AEP (see below) is placed into RCX to facilitate resuming the enclave after the exit.
Upon an AEX, the AEP (Asynchronous Exit Pointer) is loaded into the RIP. The AEP points to a trampoline code
sequence which includes the ERESUME instruction that is later used to reenter the enclave.
The following bits of RFLAGS are cleared before RFLAGS is pushed onto the exit stack: CF, PF, AF, ZF, SF, OF, RF. The
remaining bits are left unchanged.
40.2
STATE SAVING BY AEX
The State Save Area holds the processor state at the time of an AEX. To allow handling events within the enclave
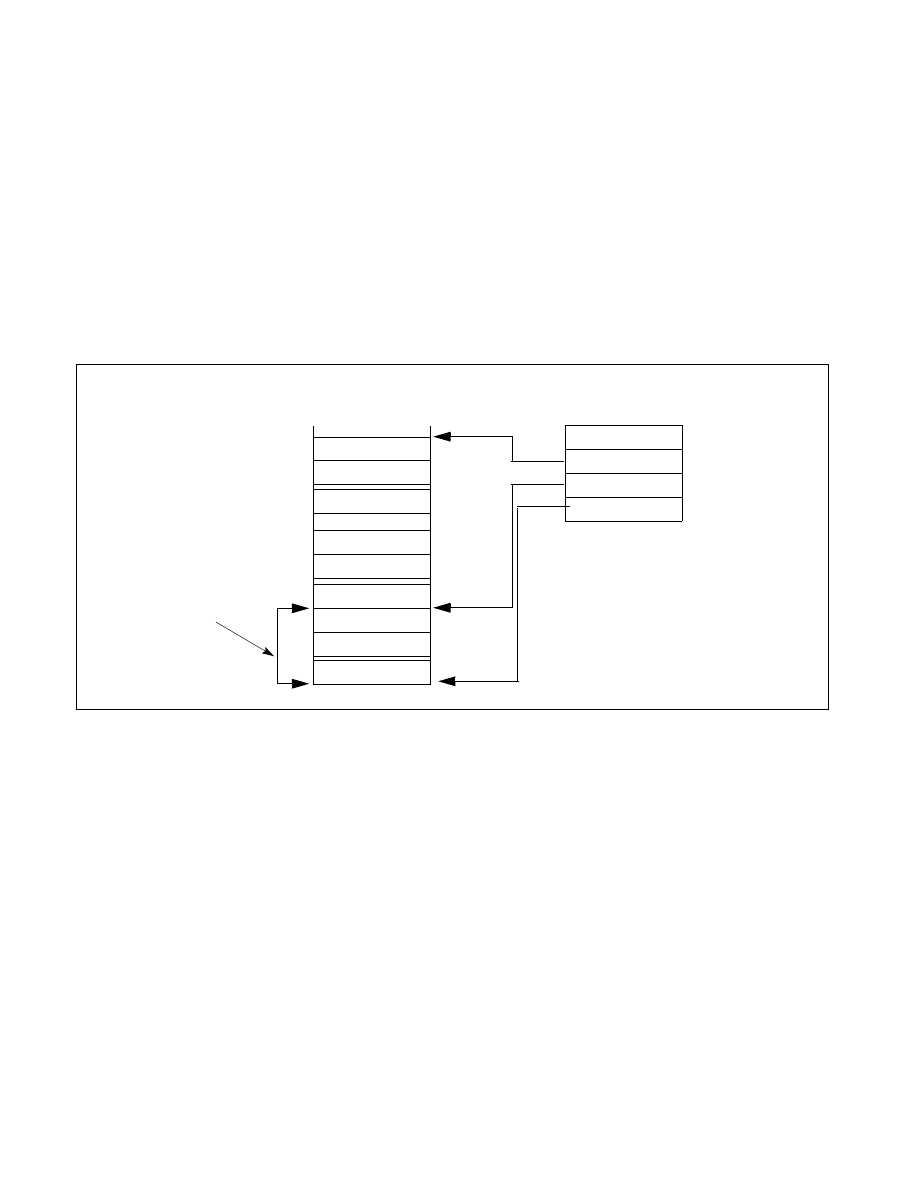
and re-entering it after an AEX, the SSA can be a stack of multiple SSA frames as illustrated in Figure 40-2.
The location of the SSA frames to be used is controlled by the following variables in the TCS and the SECS:
•
Size of a frame in the State Save Area (SECS.SSAFRAMESIZE): This defines the number of 4K Byte pages in a
single frame in the State Save Area. The SSA frame size must be large enough to hold the GPR state, the XSAVE
state, and the MISC state.
•
Base address of the enclave (SECS.BASEADDR): This defines the enclave's base linear address from which the
offset to the base of the SSA stack is calculated.
•
Number of State Save Area Slots (TCS.NSSA): This defines the total number of slots (frames) in the State Save
Area stack.
•
Current State Save Area Slot (TCS.CSSA): This defines the slot to use on the next exit.
•
State Save Area (TCS.OSSA): This defines the offset of the base address of a set of State Save Area slots from
the enclave’s base address.
When an AEX occurs, hardware selects the SSA frame to use by examining TCS.CSSA. Processor state is saved into
the SSA frame (see Section 40.4) and loaded with a synthetic state (as described in Section 40.3.1)to avoid leaking
secrets, RSP and RP are restored to their values prior to enclave entry, and TCS.CSSA is incremented. As will be
described later, if an exception takes the last slot, it will not be possible to reenter the enclave to handle the excep-
Figure 40-2. The SSA Stack
Current
SECS.SSAFRAMESIZE
TCS
NSSA
CSSA
OSSA
(in pages)
MISC_N-1
GRP_N-1
GPR_1
XSAVE_N-1
XSAVE_1
MISC_1
XAVE_0
MISC_0
GRP_0
SSA Stack
SSA Fram